Co-Managed IT: How MSPs Work Alongside Your Internal Team (Not Instead Of)
Co-managed IT services usually enter the conversation when internal teams hit a practical constraint rather than a strategic one. A migration is approaching, a new cloud architecture needs to be implemented, or a security initiative requires deeper expertise than the team currently has available. The choice then becomes straightforward. Either push through the work internally […]
Microsoft Defender and Purview: A Practical Security Operating Model

Most organizations looking at Defender and Purview integration are not building a Microsoft security stack from scratch. Chances are, they are already licensed for higher-tier Microsoft plans with add-ons, have Defender partially deployed and have Purview barely touched. That partial configuration can feel abstract, and for good reason. Defender is the threat protection layer; Purview […]
4 Signs Your Organization Is Overpaying for Microsoft Licenses
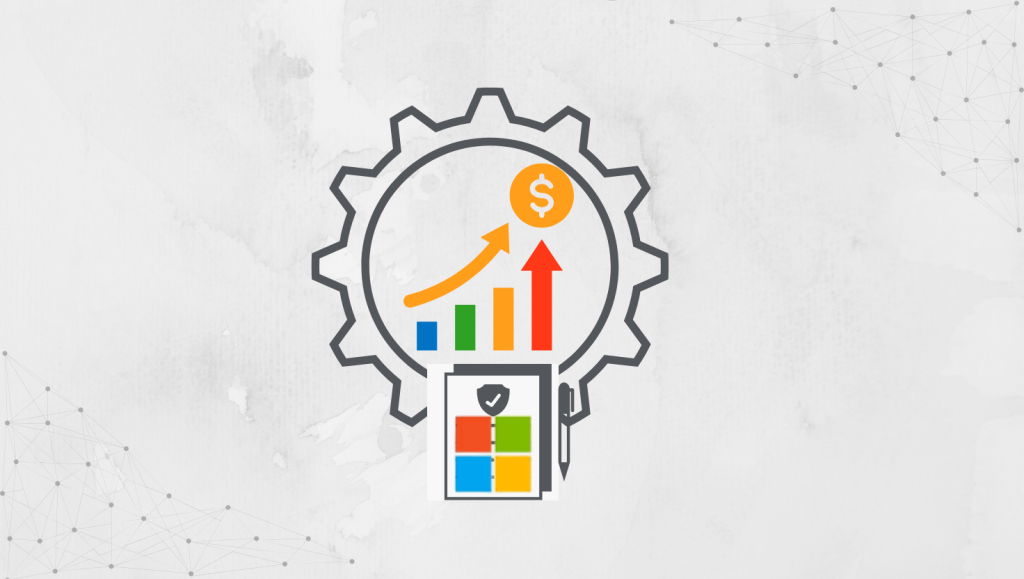
Managing Microsoft licenses in large enterprises is often straightforward in theory. Purchase the required SKUs, assign licenses efficiently, and track usage while optimizing costs. Over time, what appears structured begins to drift. Inefficiencies build, costs become less predictable, and processes lose consistency, leading to unnecessary spend. Microsoft licensing inefficiencies rarely appear at the outset. The […]
Top 7 Costly Mistakes to Avoid With Microsoft License Management

You may already suspect that you are overpaying for Microsoft licenses. However, many organizations lack visibility due to missing governance controls. At the same time, your Microsoft licensing might also be fragmented across multiple admin centers and reporting tools, none of which were designed with optimization as the primary goal. As environments grow and new […]
Microsoft License Optimization: Right-Size Your Microsoft 365 Licenses
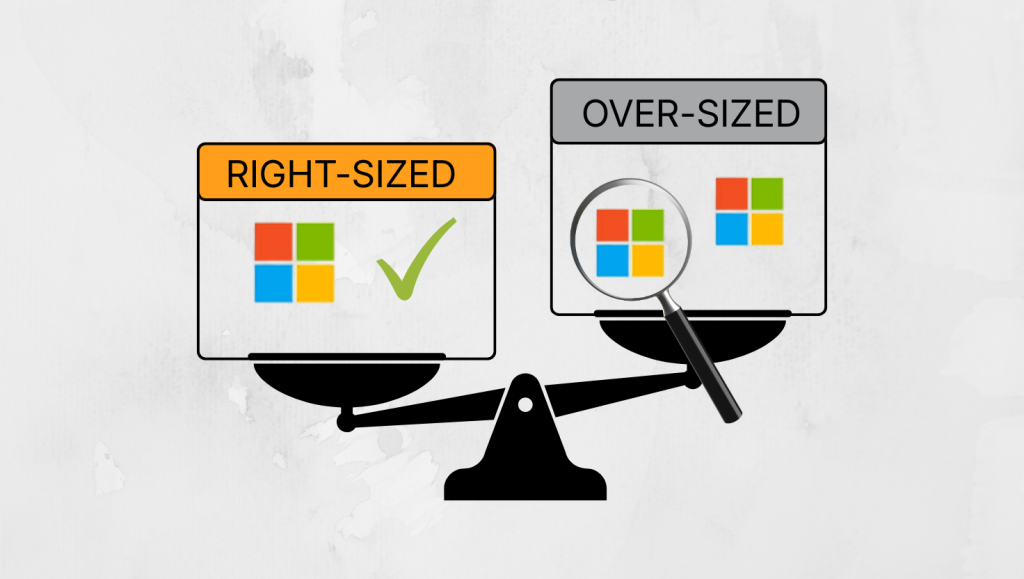
Microsoft 365 optimization usually becomes urgent when renewals are approaching. Cross-functional teams scramble to assemble reports and justify the next commitment. Reducing the number of accounts is rarely the real issue. The hidden costs often sit inside oversized licenses assigned to active employees who are not using the features included in their tier. The days […]
Microsoft 365 License Types Explained: Plans, Models and How to Choose the Right One

Microsoft 365 licensing is complex and constantly evolving. Beyond feature-driven license tiers, small and medium-sized businesses evaluating Microsoft’s cloud productivity suite often face plans that appear similar on the surface. The differences are not always obvious, yet they have meaningful implications for security, compliance, and long-term cost control. For both productivity and cost-effectiveness, choosing the […]
How to Choose a Managed Service Provider: What Really Matters (and What Doesn’t)

Choosing an IT managed service provider is about more than aligning with the right technology stack. Most MSP failures don’t arise from bad tools or wrong certifications — they stem from unclear ownership, weak SLAs and misaligned expectations that were never defined from the outset. Common customer pains that push MSP adoption affect even small […]
Microsoft Intune: Centralized Endpoint and Privilege Management
Microsoft Intune is a cloud-based endpoint management solution that enables organizations to manage end-user devices and the applications running on them. It provides centralized control over how devices are configured, secured and accessed across the organization. Even when an IT infrastructure is otherwise well secured, the weakest link is often the human element, accounting for […]
Microsoft SOC: Build In-House or Use Managed Services?

Security Operations Centers are often discussed as a capability you either have or do not. In practice, a SOC is not a binary decision. It is an operating model that must be built, staffed, governed, and sustained over time. For organizations running primarily on Microsoft 365, Azure, and identity-driven workloads, the question is not whether […]
Outlook vs Gmail Comparison: Features, Security & Pricing (2026)

Outlook vs. Gmail: A 2024 comparison to help you choose the right email for personal or business use. Discover which email platform is best for you