AI Governance in Microsoft 365: Why “Approved Tools” Is No Longer Enough

Most organizations approach AI governance as a tool problem. That model no longer holds. AI is no longer something users go to by default. It has embedded itself into the tools they already use. Treating AI governance as a tooling decision no longer reflects how AI is actually consumed. In this article, we discuss what […]
Microsoft Defender and Purview: A Practical Security Operating Model

Most organizations looking at Defender and Purview integration are not building a Microsoft security stack from scratch. Chances are, they are already licensed for higher-tier Microsoft plans with add-ons, have Defender partially deployed and have Purview barely touched. That partial configuration can feel abstract, and for good reason. Defender is the threat protection layer; Purview […]
Microsoft 365 License Types Explained: Plans, Models and How to Choose the Right One

Microsoft 365 licensing is complex and constantly evolving. Beyond feature-driven license tiers, small and medium-sized businesses evaluating Microsoft’s cloud productivity suite often face plans that appear similar on the surface. The differences are not always obvious, yet they have meaningful implications for security, compliance, and long-term cost control. For both productivity and cost-effectiveness, choosing the […]
Outlook vs Gmail Comparison: Features, Security & Pricing (2026)

Outlook vs. Gmail: A 2024 comparison to help you choose the right email for personal or business use. Discover which email platform is best for you
Cybersecurity Trends in 2026: Microsoft Developments to Watch
Companies across the globe are faced with a ballooning number of cybersecurity breaches. Discover the top 7 cybersecurity trends in 2024.
Microsoft Managed Services Explained: Security, Governance and Control

Microsoft managed services is a term that carries multiple interpretations. For some organizations, it means managing their Office 365 environment. For others, it extends to Azure, IT infrastructure management, and mobile device management. Most guides fall into one of two categories: they are vendor-led pitches presented as education, or they focus heavily on what is […]
Securing SharePoint Post-Migration: Top 5 Governance Considerations

SharePoint migration doesn’t end when content is moved to the new environment. In many organizations, it’s actually the point where security risk begins to build. Permissions can expand, external sharing may become harder to monitor, and the governance controls established during migration often weaken over time. Post-migration security requires a governance plan to keep your data secure. Without governance, SharePoint environments retain legacy access models, overshared content and inconsistent controls that no longer […]
Microsoft 365 E3 vs E5: Compare Plans & Pricing
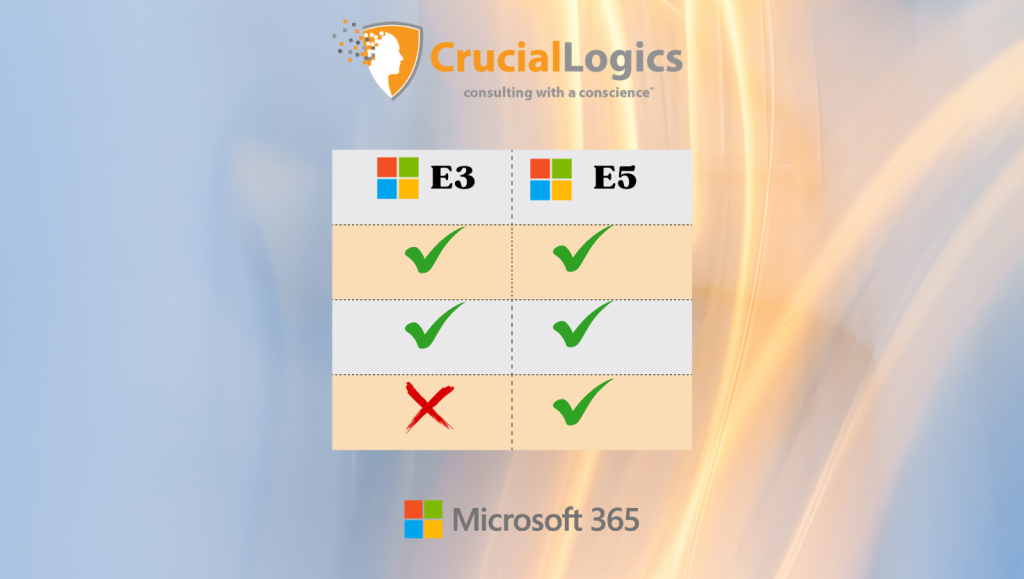
Microsoft 365 comes with a wide range of tools that help teams collaborate smoothly, share files easily, and stay productive across the organization. To get the most value from it, you need a licensing plan that aligns with your operational needs and budget. For larger organizations, the two main enterprise options are Microsoft 365 E3 […]
Maximizing Efficiency With Granular Delegated Admin Privileges (GDAP)
Granular Delegated Admin Privileges (GDAP) is a Microsoft security feature that enables managed service providers (MSPs) to manage customer environments following the principle of least privilege access. Think of GDAP like giving someone a spare key to your house but only for certain rooms and only for a limited time. In this blog, we’ll outline […]
Microsoft Edge vs Chrome: Why IT Admins Choose Edge

Microsoft Edge and Google Chrome are powerful web browsers, feature-packed and with a constant lineup of updates. However, only one can dominate your end-users’ browsing experience. From an end-user perspective, switching to Microsoft Edge shouldn’t feel like a downgrade. In many ways, it feels the same as Chrome (since they share the same engine) with a […]


