Mirador Managed Defense MXDR
Advanced security protection
Mirador Managed Defense MXDR (Advanced Managed Extended Detection and Response) combines Mirador Managed Defense MDR and Mirador Managed Defense SEIM while integrating with Microsoft Sentinel and Microsoft Defender solutions (Microsoft Defender for Endpoint, Microsoft 365 Defender, Microsoft Defender for Cloud) to enhance your organization’s cybersecurity posture while having access to industry experts to take your security to a new level.
Get Started Today

Why Use CrucialLogics?
INTEGRATION WITH MICROSOFT SENTINEL SIEM
Stream all Microsoft 365 Defender incidents into Microsoft Sentinel to synchronize between both portals. Incidents from Microsoft 365 Defender include all associated alerts, entities, and relevant information, providing you with enough context to perform triage and preliminary investigation in Microsoft Sentinel.
INTEGRATION WITH MICROSOFT XDR
All Defender (Extended Detection and Response) solutions, such as Microsoft Defender for Cloud and Microsoft 365 Defenders, help protect against advanced attacks. Enhanced threat visibility and protection are delivered efficiently through Microsoft native integrations such as Defender for Threat Intelligence, Defender for External Attack Surface Management (EASM) and NDR through Microsoft ISV VECTRA or any third-party security solutions.
CONSOLIDATED THREAT MONITORING
Combine endpoint, cloud resource, dark web, and network monitoring for malware detection and incident response into a single solution.
ADVANCED AUTOMATED RESPONSE
Benefit from automated playbooks across Microsoft Sentinel and Microsoft Defender for Endpoint, including endpoint isolation, full AV scans, disable AD user and user password resets.
ADVANCED THREAT DETECTION AND REPORTING
Round-the-clock monitoring SIEM 24/7/365 SOC-As-A-Service ensures readiness to respond to any cyber threat. Perform monthly threat hunts based on asset-based threat intelligence and triggered incidents. Comprehensive incident triage and investigation reports are provided.
DASHBOARDS
Use global and dedicated custom dashboards to view security posture and gain insights into critical security data to make informed decisions.
GET SECURE TODAY
Testimonials
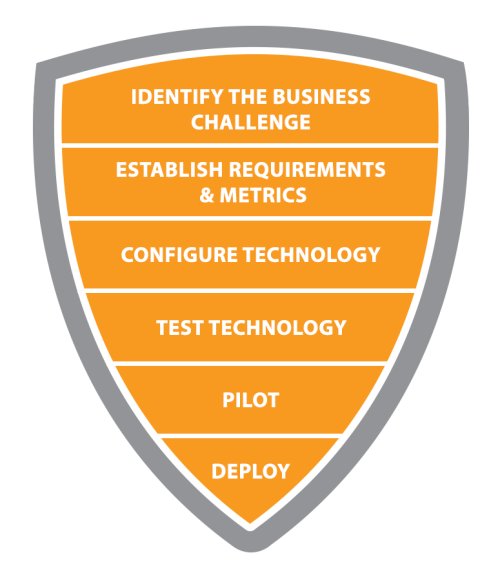
How We Work
We remove the barriers that make cybersecurity complex. We deeply understand attacker behaviour and how to secure against them.