Outlook vs Gmail Comparison: Features, Security & Pricing (2026)

Outlook vs. Gmail: A 2024 comparison to help you choose the right email for personal or business use. Discover which email platform is best for you
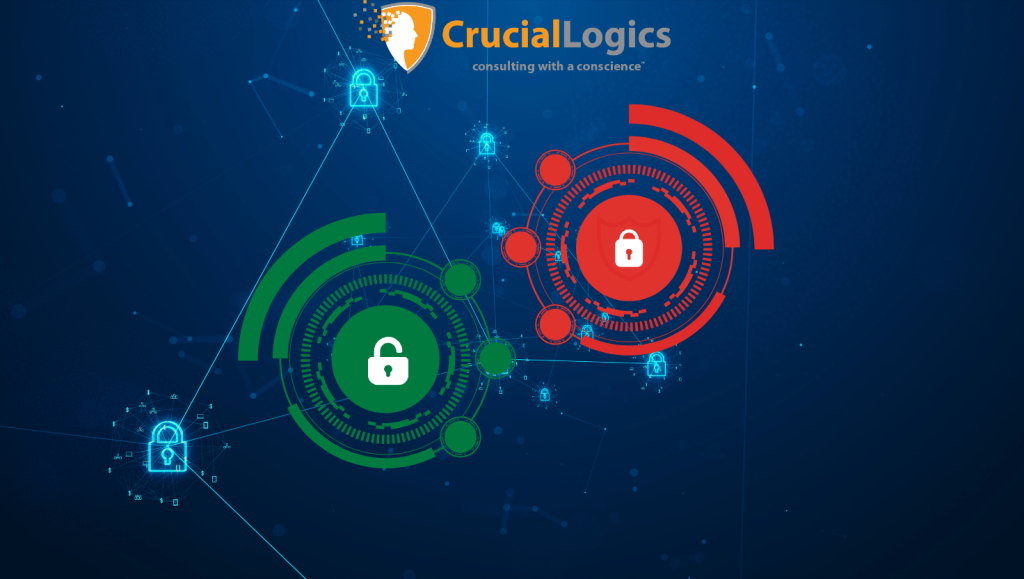
Cybersecurity Trends in 2026: Microsoft Developments to Watch
Companies across the globe are faced with a ballooning number of cybersecurity breaches. Discover the top 7 cybersecurity trends in 2024.
Microsoft Managed Services Explained: Security, Governance and Control

Microsoft managed services is a term that carries multiple interpretations. For some organizations, it means managing their Office 365 environment. For others, it extends to Azure, IT infrastructure management, and mobile device management. Most guides fall into one of two categories: they are vendor-led pitches presented as education, or they focus heavily on what is […]
Modernize Your Workplace: Building a Secure SharePoint Intranet

SharePoint is a core product for companies using Microsoft 365. Sitting at the heart of collaboration, it acts as a centralized information repository that connects Teams, Outlook, Viva Engage and the rest of the Microsoft 365 tools. Broadly, there are two types of SharePoint sites: communication sites and team sites. A communication site, often referred […]
Securing SharePoint Post-Migration: Top 5 Governance Considerations

SharePoint migration doesn’t end when content is moved to the new environment. In many organizations, it’s actually the point where security risk begins to build. Permissions can expand, external sharing may become harder to monitor, and the governance controls established during migration often weaken over time. Post-migration security requires a governance plan to keep your data secure. Without governance, SharePoint environments retain legacy access models, overshared content and inconsistent controls that no longer […]
Four Common Managed IT Challenges and How to Avoid Them

Managed IT services help keep your IT infrastructure running smoothly, reduce bottlenecks, and maintain your systems. With the rise of hybrid work environments, managed IT environments have become increasingly complex. This complexity can create major barriers to business growth because poor IT service management directly impacts operational efficiency. When a solution designed to simplify IT becomes a challenge of […]
How to Design a Microsoft Security Architecture Using Azure, Microsoft 365 & AI

Microsoft is one of the largest software vendors that provides customers with a security-focused public cloud platform. With a broad range of technologies and security tools that can fit small, medium and large enterprises, Microsoft lays a solid foundation for a modern IT environment. For most businesses, however, the problem is not adoption. Reliable third-party […]
AI Security: Using Microsoft 365 Copilot Safely at Scale

AI productivity assistants and task-driven agents are becoming part of daily operations across most large organizations. Regardless of form, one question remains: how can organizations secure AI and govern it at scale? The most common issues include exposure of sensitive data, increased strain on IT teams, compliance gaps and uncontrolled information sharing across the organization. […]
Microsoft 365 E3 vs E5: Compare Plans & Pricing
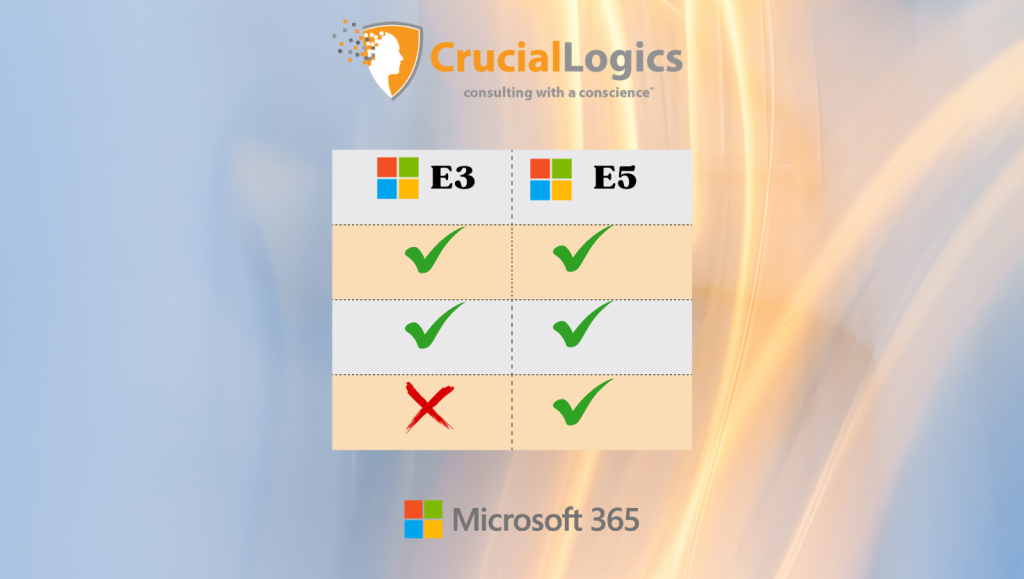
Microsoft 365 comes with a wide range of tools that help teams collaborate smoothly, share files easily, and stay productive across the organization. To get the most value from it, you need a licensing plan that aligns with your operational needs and budget. For larger organizations, the two main enterprise options are Microsoft 365 E3 […]
Maximizing Efficiency With Granular Delegated Admin Privileges (GDAP)
Granular Delegated Admin Privileges (GDAP) is a Microsoft security feature that enables managed service providers (MSPs) to manage customer environments following the principle of least privilege access. Think of GDAP like giving someone a spare key to your house but only for certain rooms and only for a limited time. In this blog, we’ll outline […]