Cloud Security Assessment
Evaluate Your Security Posture
Evaluate Your
Security Posture
Our comprehensive assessments use Critical Security Controls (CIS) version 8 to thoroughly evaluate your environment, including configuration, security baselines, and other key features. This provides you with a comprehensive understanding of your current security posture and any potential vulnerabilities.
Book Your Assessment Today

Why Use CrucialLogics for Assessments?
ACTIONABLE RECOMMENDATIONS
Receive a detailed report with actionable recommendations to address identified vulnerabilities and implement the necessary security controls to mitigate the risk of cyber threats and data breaches.
COMPLIANCE REQUIREMENTS
Ensure compliance with regulatory requirements such as NIST, FIPA/HIPAA, PCI-DSS, GDPR and more.
ENHANCED SECURITY POSTURE
Get peace of mind knowing that you are up-to-date and secure.
COST-EFFECTIVE SOLUTION
You receive competitive pricing and flexible engagement options to meet your needs.
TRUSTED PARTNER
As a Microsoft Advance Specialized Partner in Cloud and Threat Protection, our team has a proven track record of delivering high-quality Microsoft security services.
Our clients trust us to provide the best possible service and support, and we take that responsibility seriously.
We offer assessments in

- Policies and settings: device enrollment policies, app management policies, and compliance policies
- Configuration profiles: endpoint devices such as laptops, desktops, and mobile devices
- Security baselines: security settings and configurations for endpoint devices managed by Intune
- Conditional access: control access to your corporate resources based on a set of conditions such as device compliance and user identity
- App protection policies: data encryption and app-level restrictions for mobile devices

- Security features: Attack Surface Reduction (ASR), threat protection, and access controls
- Tenant configuration: device management, endpoint protection, and threat and vulnerability management
- Policies and settings: device protection policies, email and file protection policies, and device management policies
- Compliance and regulatory assessment: adherence to NIST, FIPA/HIPAA, PCI-DSS, and GDPR, and Microsoft's standards
- Collaboration security controls: Settings and access controls for Microsoft Teams, OneDrive for Business, and SharePoint Online

- Security features: multi-factor authentication (MFA), data loss prevention (DLP), and access controls
- Security configurations: audit logging, threat management, and encryption
- Tenant configuration: settings for user and group management including Exchange Online, SharePoint Online, and OneDrive for Business
- Policies and settings: password policies, email retention policies, and device management policies
- Collaboration security controls: security settings and review use of OneDrive for Business, SharePoint Online, and Microsoft Teams
Evaluate your Security
Testimonials

“When we announced CrucialLogics HyperCare as our new on-site support solution to our workforce, the entire room burst into applause.”

CrucialLogics gave a fulsome presentation and delivered on it. Their knowledge base has been strong and the experience of working with them has been good.
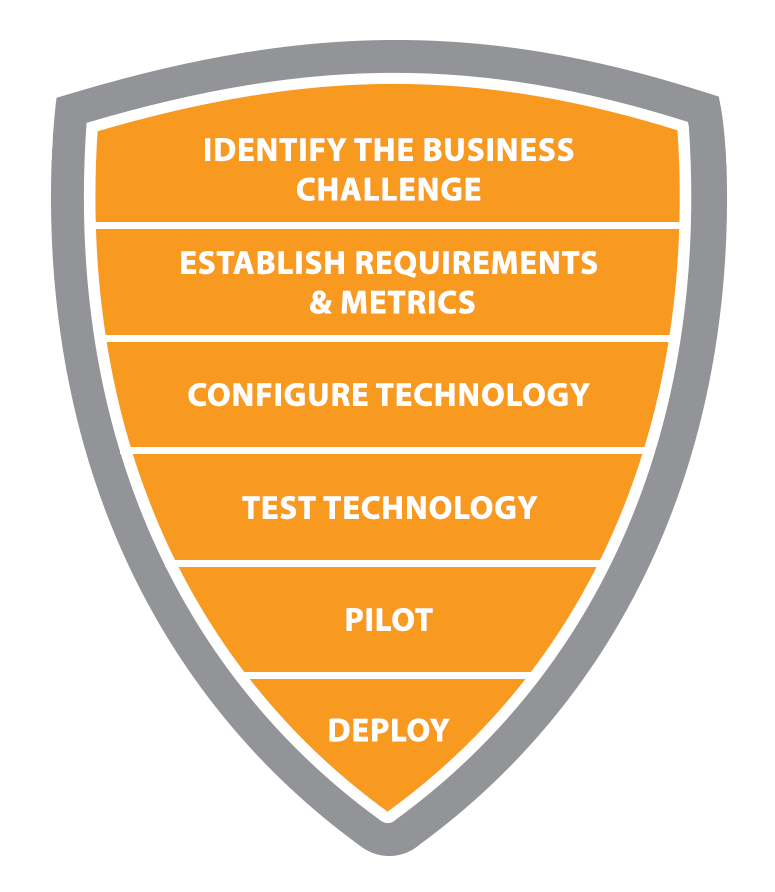
How We Work
We remove the barriers that make cybersecurity complex. We deeply understand attacker behaviour and how to secure against them.